Web-based Terminal¶
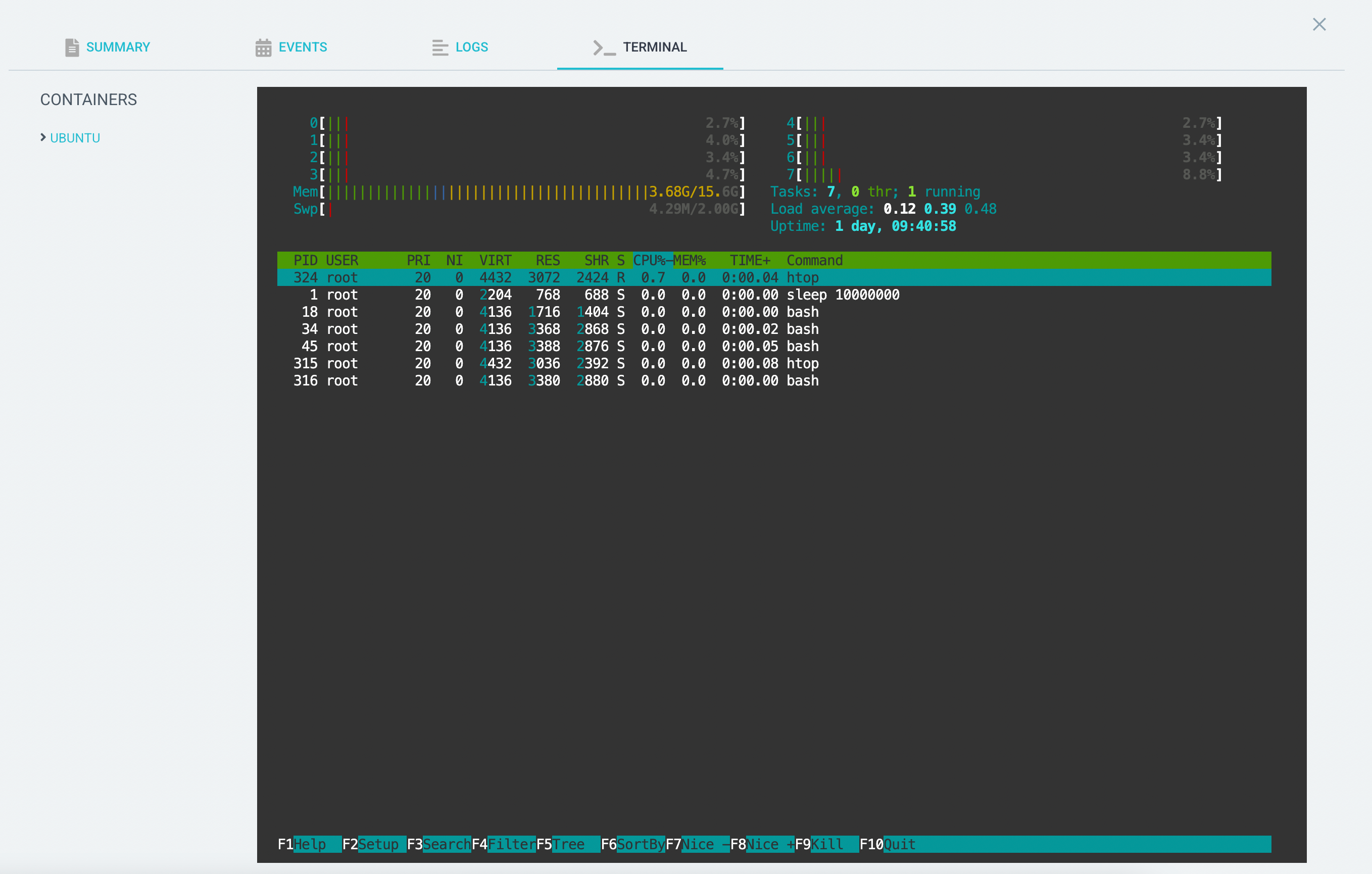
Since v2.4, Argo CD has a web-based terminal that allows you to get a shell inside a running pod just like you would with
kubectl exec. It's basically SSH from your browser, full ANSI color support and all! However, for security this feature
is disabled by default.
This is a powerful privilege. It allows the user to run arbitrary code on any Pod managed by an Application for which
they have the exec/create privilege. If the Pod mounts a ServiceAccount token (which is the default behavior of
Kubernetes), then the user effectively has the same privileges as that ServiceAccount.
Enabling the terminal¶
-
Set the
exec.enabledkey to"true"on theargocd-cmConfigMap. -
Patch the
argocd-serverRole (if using namespaced Argo) or ClusterRole (if using clustered Argo) to allowargocd-serverto exec into pods- apiGroups: - "" resources: - pods/exec verbs: - create -
Add RBAC rules to allow your users to
createtheexecresource, i.e.p, role:myrole, exec, create, */*, allow
See RBAC Configuration for more info.
Changing allowed shells¶
By default, Argo CD attempts to execute shells in this order:
- bash
- sh
- powershell
- cmd
If none of the shells are found, the terminal session will fail. To add to or change the allowed shells, change the
exec.shells key in the argocd-cm ConfigMap, separating them with commas.